CISA Warns of Langflow Code Injection Vulnerability Exploited in Attacks
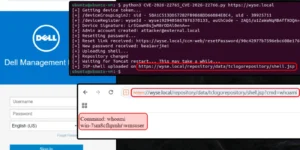
The Cybersecurity and Infrastructure Security Agency (CISA) has officially added a critical security flaw affecting the Langflow platform to its Known Exploited Vulnerabilities (KEV) catalog on March 25, 2026. The …