Magecart Hackers Uses 100+ Domains to Hijack eStores Checkouts and Steal Card Data
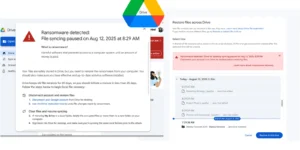
A sophisticated and long-running Magecart campaign has been quietly operating for over 24 months, infecting e-commerce websites across at least 12 countries using more than 100 malicious domains to steal …